SSL Configuration in QuickFIX/n
In this guide, we will cover the process of configuring SSL (Secure Socket Layer) for the FIX (Financial Information Exchange) protocol using the QuickFIX/n library in C#. Secure communication is vital in financial transactions, and SSL is a key component in ensuring data integrity and confidentiality.
Here is the list of topics this guide covers:
- Acquiring and installing SSL certificates.
- Modifying QuickFIX/n settings for SSL support.
- Establishing and testing secure FIX sessions.
Acquiring and installing SSL certificates
The first step in securing FIX sessions is to acquire and install SSL certificates. SSL certificates are digital certificates that authenticate the identity of a website and enable an encrypted connection.
For local development and testing, SSL certificates can often be self-signed and stored in a specific folder on your machine. See Generating self-signed FIX SSL certificates article for details on how to generate such certificates. This approach is convenient for initial stages of development but should not be used in production due to the lack of proper validation and trust.
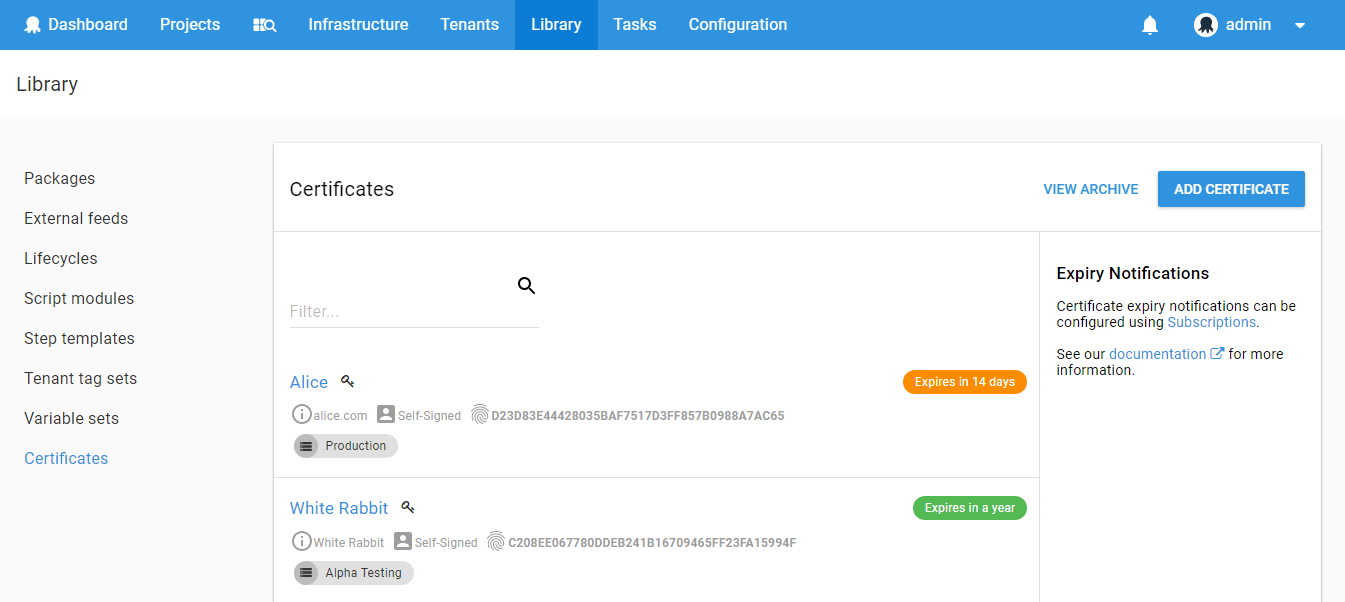
For production environments, it's essential to acquire SSL certificates from a reputable Certificate Authority (CA). Once acquired, these certificates need to be installed on the server where the FIX application will run. The process of installing and updating these certificates can be automated and managed through a CI/CD pipeline. Tools like Octopus Deploy can be configured to handle certificate installation, ensuring they are kept up-to-date and renewing them before they expire. Automated notifications can be set up to alert administrators of upcoming expiry dates, reducing the risk of service interruptions due to expired certificates. Here is how SSL certificate management looks in Octopus (https://octopus.com/docs/deployments/certificates)
It's crucial to have a process in place for managing SSL certificates effectively, as they are the cornerstone of securing communication in FIX sessions.
Modifying QuickFIX/n settings for SSL support
Next, we need to modify our FixApp.cfg file to add the following lines:
SSLEnable=Y
SSLProtocols=Tls12
SSLCertificate=#{FIX_SSL_Certificate_Name}
SSLServerName=#{FIX_SSL_ServerName}
SSLValidateCertificates=Y
SSLCheckCertificateRevocation=Y
The parameters in the configuration, denoted by #{...}, are placeholders meant to be dynamically replaced with actual values during the deployment process. This setup is typically managed through a Continuous Integration/Continuous Deployment (CI/CD) solution. By using this approach, sensitive information such as SSL certificate names and server names can be securely managed and injected at deployment time, ensuring that configuration files do not expose critical data in their static form.
Here is a brief description of the properties:
- SSLEnable: Enables SSL encryption for the connection. Set to 'Y' to enable.
- SSLProtocols: Defines the SSL protocol to use, e.g., Tls12 for TLS version 1.2.
- SSLCertificate: The name of the SSL certificate file used for the connection. The placeholder
#{FIX_SSL_Certificate_Name}should be replaced with the actual certificate name during the CI/CD process. - SSLServerName: The server name for SSL verification. The placeholder
#{FIX_SSL_ServerName}should be replaced with the actual server name during the CI/CD process. - SSLValidateCertificates: Enables validation of SSL certificates. Set to 'Y' to enable.
- SSLCheckCertificateRevocation: Enables the checking of SSL certificate revocation. Set to 'Y' to enable.
For development, when you use self-signed certificates, it's often convenient to use a path to a certificate file instead of a name. In this case, configuration would be as follows:
SSLEnable=Y
SSLCertificate=D:\Certificates\PROJECT\project-fix-dev.pfx
SSLCertificatePassword=SECRET
project-fix-dev.pfx is a P12 file with both public and private keys, and SSLCertificatePassword is a password for this file.
For other SSL-related setting in QuickFIX, refer to the official documentation: https://new.quickfixn.org/n/documentation/#item-ssl-4.
This setup ensures that all data transmitted over FIX sessions is encrypted, providing confidentiality and integrity in financial messaging.